Simple Explanation of Symantec Zero Trust Network Access (ZTNA) Capabilities
Zero Trust Network Access (ZTNA) is a modern approach to secure access to applications and data. Unlike traditional VPNs, ZTNA trusts no one by default – every user, device, and request must be verified before access is granted.
The goal is simple: to provide secure, controlled, and fast access to applications without opening the entire network.
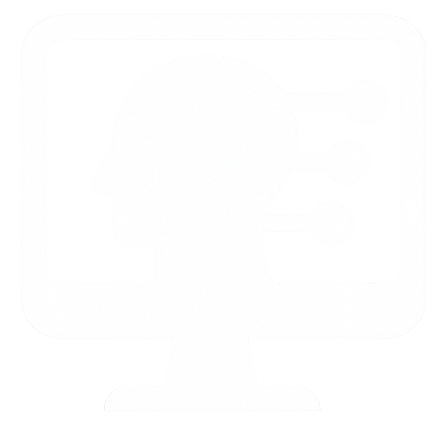
Perimeterless World
Applications are no longer confined to corporate networks — they’re scattered across datacenters worldwide, accessed by users from any location and any device. Traditional perimeter-based security can’t keep up.
Secure Native Access
Symantec ZTNA enables secure RDP and SSH access without opening inbound ports or relying on legacy perimeter controls. Users launch their native RDP or SSH clients as usual, while ZTNA brokers the connection through identity verification, device posture checks, and continuous trust evaluation. This preserves the native workflow while ensuring every session is authenticated, authorized, and inspected before reaching internal systems.
Secure Access for BYOD
Symantec ZTNA enables secure access from unmanaged devices by shifting trust away from the endpoint and into the access layer. Instead of relying on device ownership, ZTNA validates user identity, applies browser‑based isolation, and enforces granular access policies before any session reaches internal applications. This allows users to connect from any device while ensuring that sensitive systems remain protected from untrusted endpoints.
What do you do when the network perimeter disappears?
When the network perimeter disappears, you shift from protecting locations to protecting identities, devices, and the applications themselves — enforcing access based on who the user is, the context of the request, and the trustworthiness of the device rather than where the connection originates.

Implementing DLP on internal applications
Implementing DLP on internal applications with Symantec ZTNA means inspecting and controlling sensitive data directly within the secure access path, apply DLP policies to internal web traffic before it reaches the user

Threat Protection Integration
Threat Protection integration in Symantec ZTNA enables inline inspection of web application traffic using Threat Inspection Service (TIS), allowing organizations to detect and quarantine suspicious activity before it reaches internal resources.
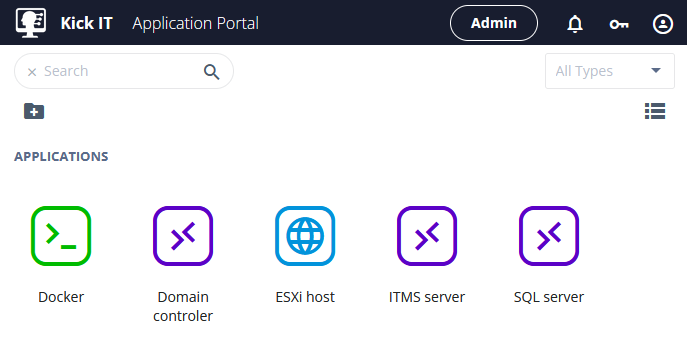
Accessing internal web applications
User portal access makes it easy to reach your internal web apps from any modern browser, with a clean, intuitive interface that lets users open authorized resources instantly.
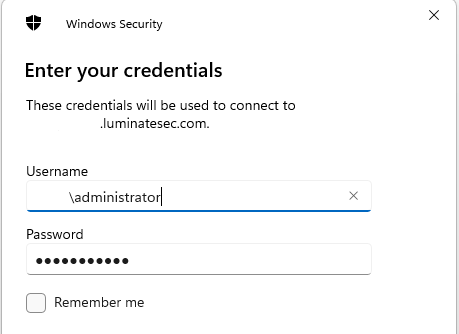
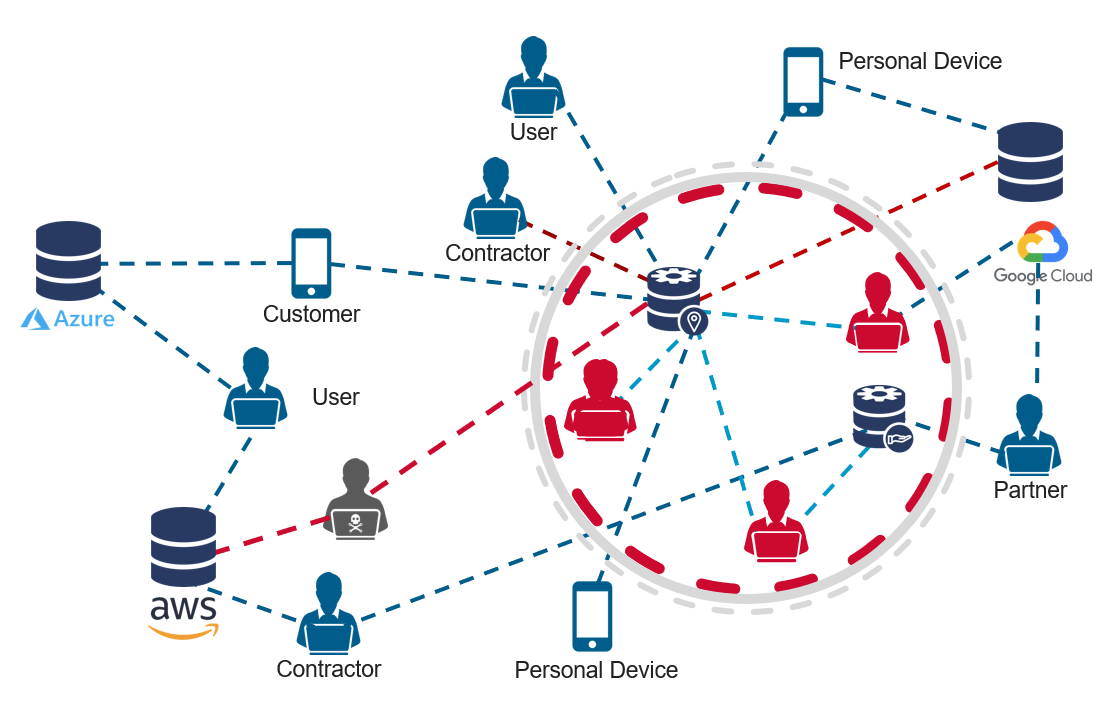
RDP access
RDP access is equally straightforward, letting users open authorized internal RDP desktops or servers using native tools while initiating the session
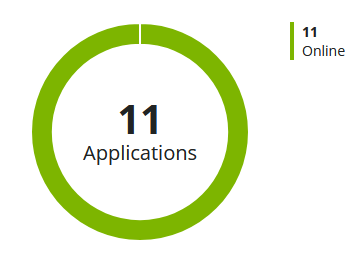
Application availability monitoring
Application availability monitoring provides continuous insight into whether protected applications and sites are reachable and performing normally, with instant detection of outages, slow response, or degraded service quality.
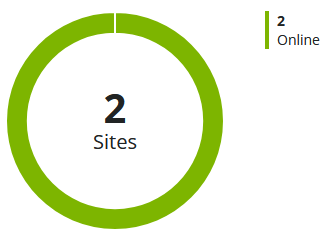
Connector status tracking
Connector status tracking ensures continuous visibility into the health and connectivity of distributed ZTNA sites, enabling proactive response to outages, latency, or degraded performance.
User portal access
User portal access is designed for simplicity, giving users a clean, intuitive interface where they can reach authorized applications instantly without navigating complex menus or legacy VPN workflows

SSH access
SSH access is just as seamless, allowing users to reach authorized internal SSH endpoints directly from any modern browser through a simple, intuitive interface